Azure Active Directory | Cross tenant synchronization
These days are more and more companies working in Azure Active Directory. They are using Azure AD Connect to synchronize those accounts from on-premises Active Directory to Azure Active Directory. When a company is acquiring a new company and they acquired company need to access the applications or data in the Target company, you could create guest users in Azure Active Directory for those users. But when there are over 200 users, doing this manually will give a huge workload.
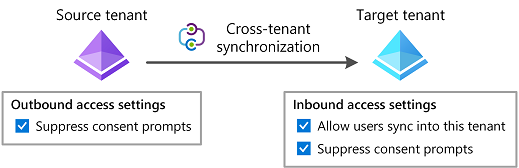
A new feature, in preview, in Azure Active Directory is: Cross tenant synchronization. In basics this is a Azure B2B. Provision the users from the acquired company tenant to the new Target Company tenant. It will create a B2B member user with all the properties from the source tenant.
Accessing applications in the target tenant with a Azure B2B account from the source tenant without user consent to accept the invitation. Joiners and leavers are automatically added and deleted.
Setup Target tenant
In basic the connection between the tenant is using an app registration. Normally you would create it yourself, but this time it will be created automatically when setting up the connection. Browsing to Azure Active Directory – External Identities
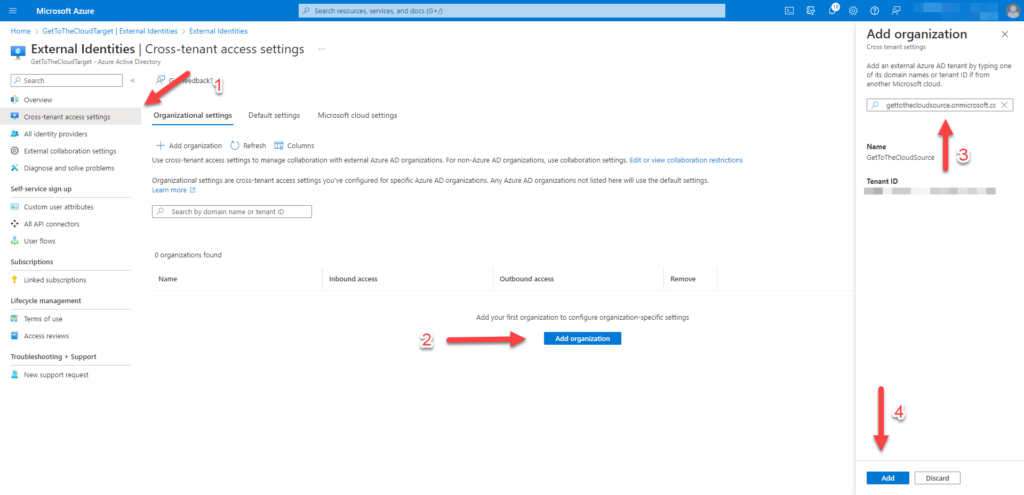
Adding the external .onmicrosoft.com organization will ensure that the correct tenant is connected.
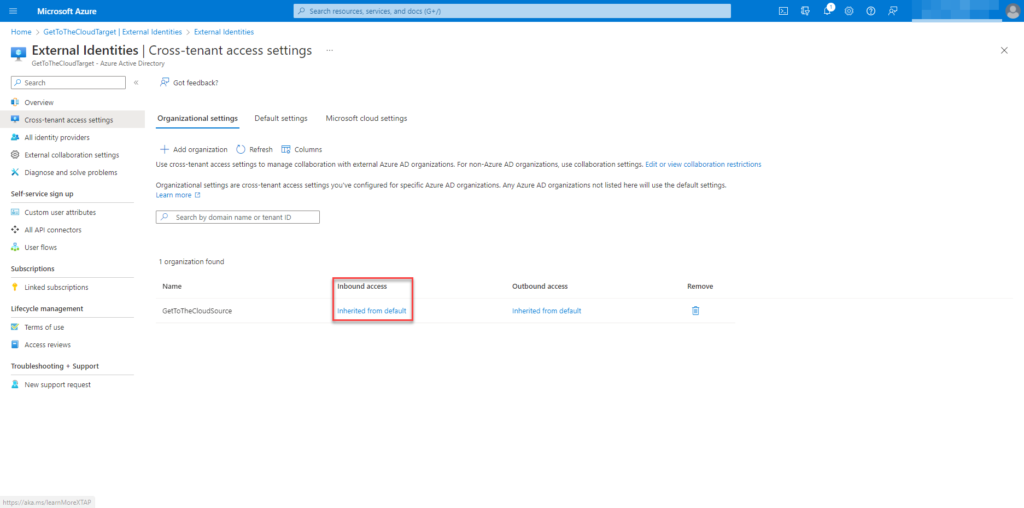
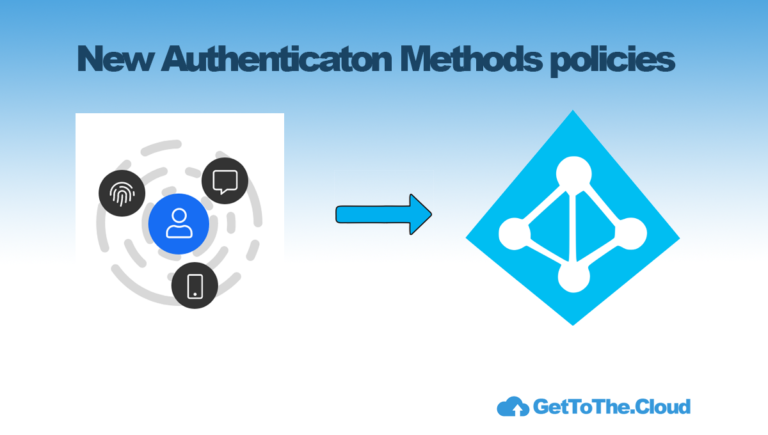
Configure Inbound Access to set the correct permissions
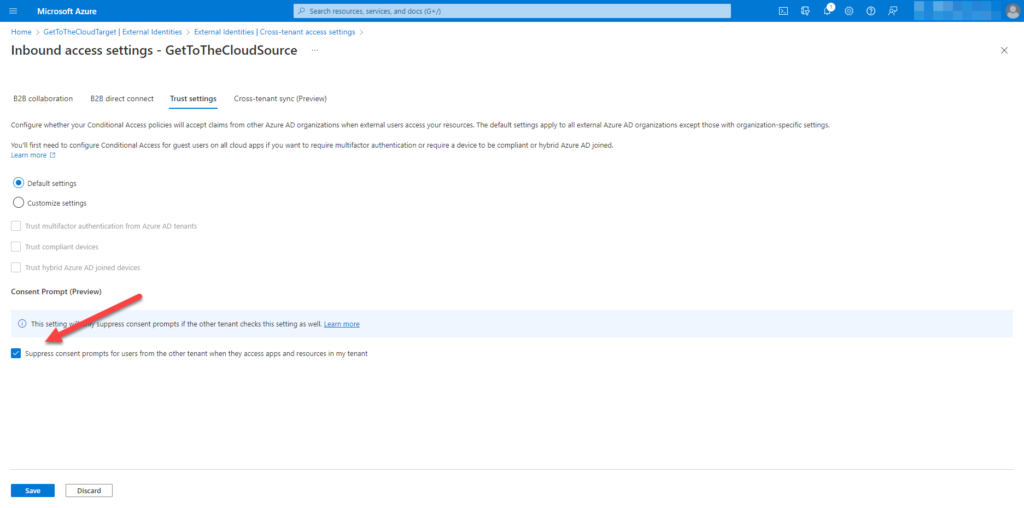
Browsing to Trust settings will give the option to select Suppress consent prompts for users from the other tenant when they access apps and resources in my tenant.
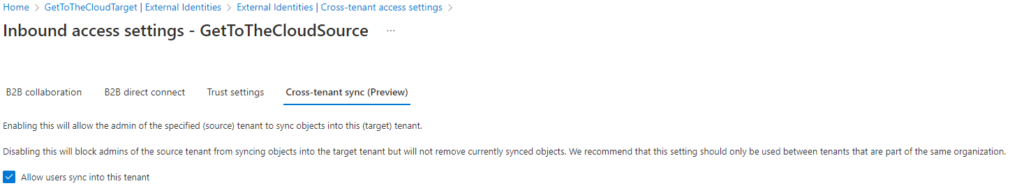
Browse to Cross-tenant sync (preview) and select Allow users sync into this tenant,
Setup Source tenant
This is the tenant where from the identities will be synced to the new tenant
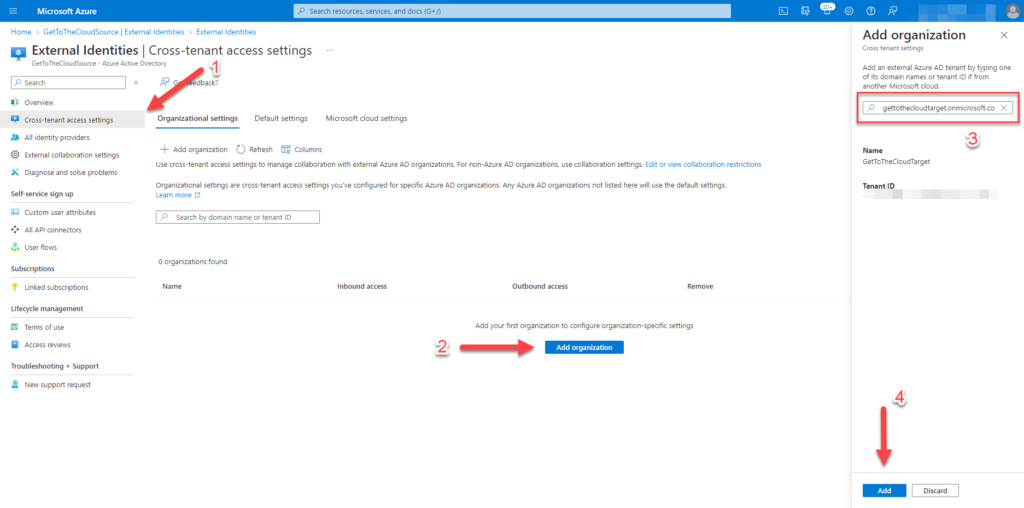
Adding the external .onmicrosoft.com organization will ensure that the correct tenant is connected.
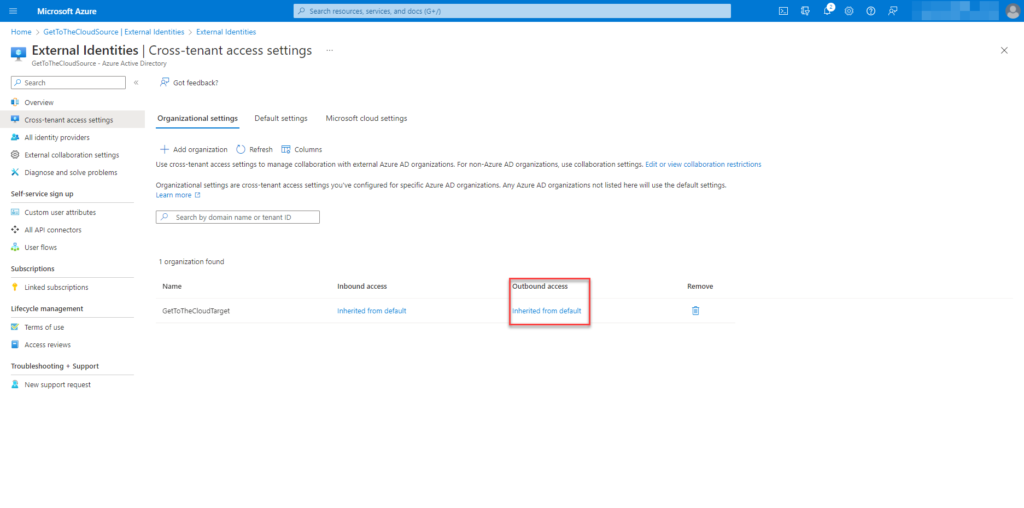
Configure Outbound Access to set the correct permissions
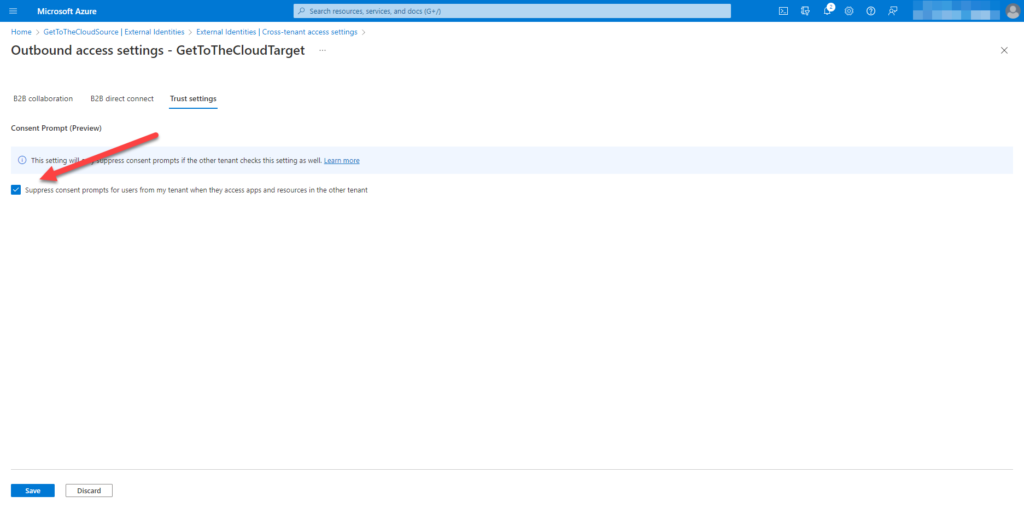
Browsing to Trust settings will give the option to select Suppress consent prompts for users from the other tenant when they access apps and resources in my tenant.
Setting up the synchronization
Login to the SourceTenant and browse to Azure Active Directory. There you will find Cross-tenant synchronization (preview).
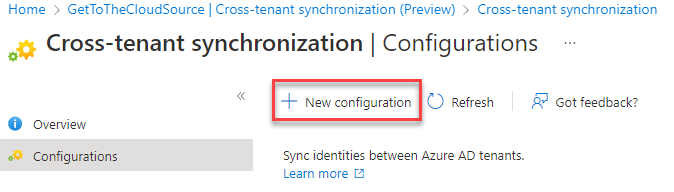
Select New configuration
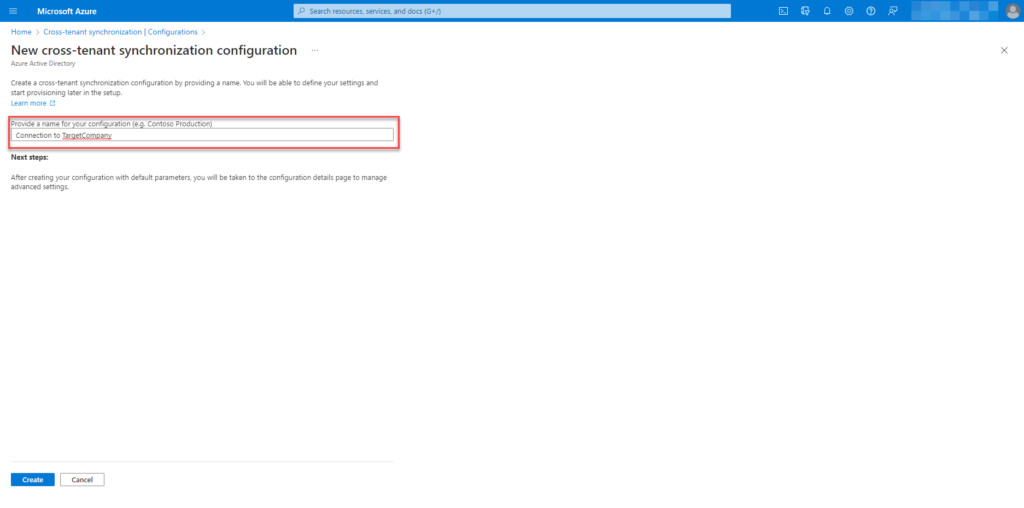
Enter a name for the configuration
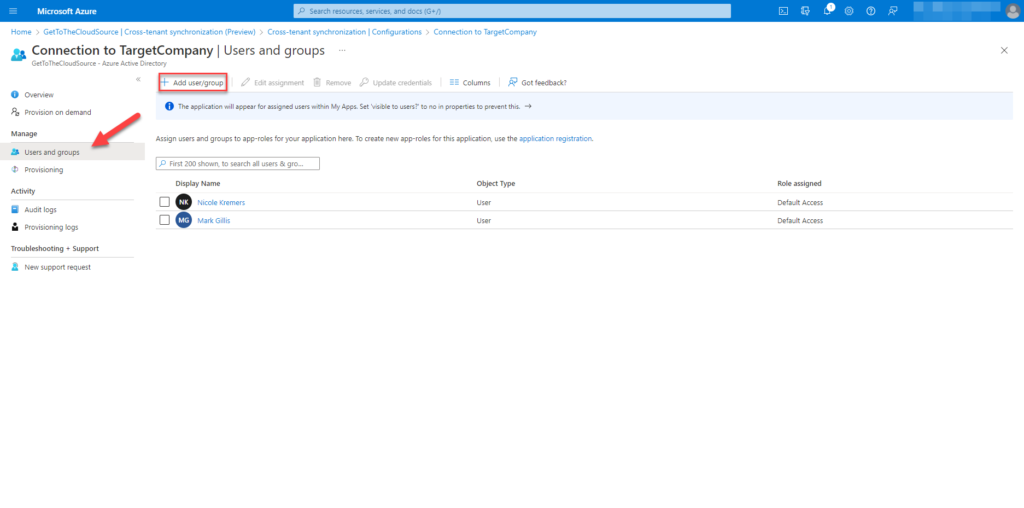
When browsing to the configuration, we are able to add users/groups for provisioning. Every member in the group selected will be synchronized.
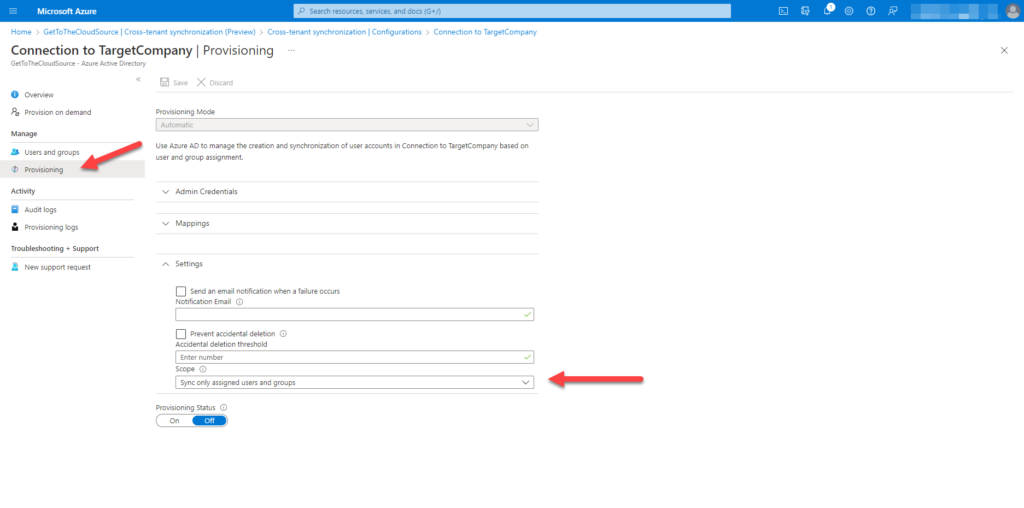
Browsing to Provisioning, set the Scope to Sync only assigned users and groups. There is also a possibility to Sync all users and groups. Switch the Provisioning Status to On.
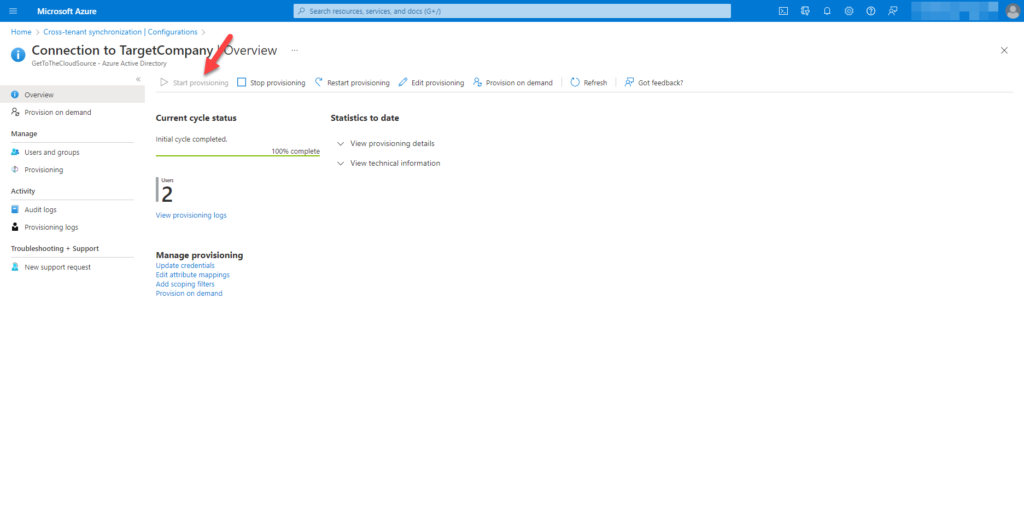
If it is needed you can select Start provisioning. The results will be as stated.
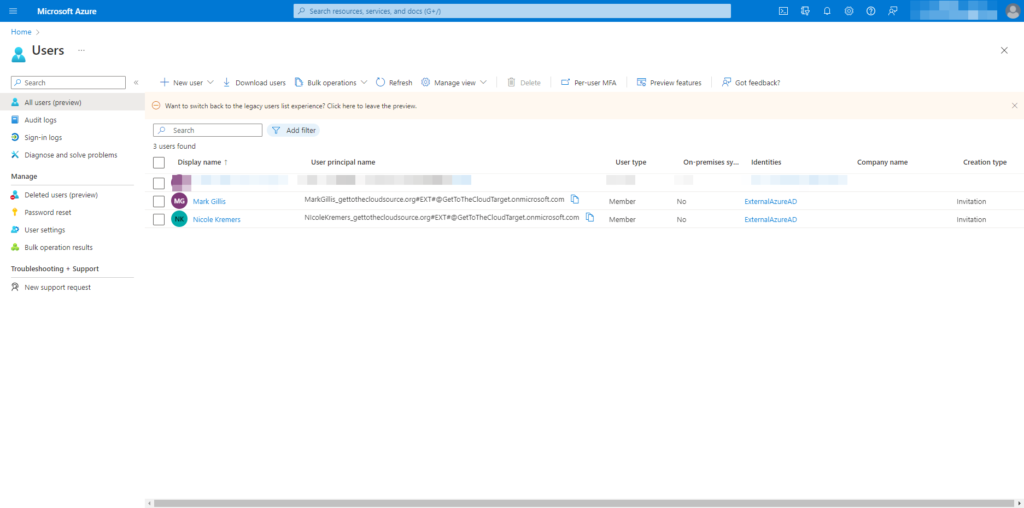
Logging in to the TargetCompany tenant you will see the users are provisioned